October 20, 2014
Blackhat Europe: Attacking /dev/urandom on Android
Our paper was accepted to both Usenix WOOT and Blackhat Europe! So Nadja and I got to go to Amsterdam :) !
We wanted to exploit CVE-2014-3100 - a stack based buffer overflow in Android’s Keystore.
We needed to bypass the stack canary.
Long story short, we devised probablistic attacks that enables an attacker to
predict random bytes that are extracted from the
underlying entropy pool of /dev/urandom during device boot, such as Keystore’s canary value.
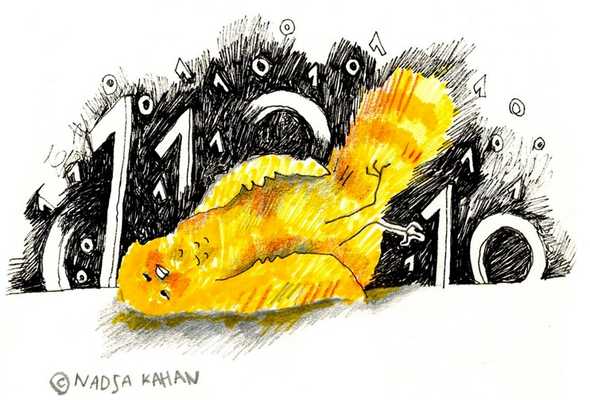
I explained the attack to Nadja and the result was a dead canary drawing:
Never have I spoken to so many people, let alone in a foriegn language. It was a daunting, yet necessary, baptism of fire.
Here’s the video:
[slides] [paper]Here is a picture of Adi Shamir and I. We’ve met in the speaker’s lounge. He also attended my talk!

